Blogs

Introduction In today’s interconnected global economy, secure financial transactions are the backbone of trust and reliability. Every day, banks and financial institutions exchange billions of…

Understanding the Basics: What Are SOC 2 and SOX? In today’s highly interconnected business environment, trust, security, and transparency are more important than ever. To…

In today’s technology-driven world, cybersecurity is typically linked to tools like firewalls, encryption, software updates, and password protection. While these elements are essential for safeguarding…
"Do I need a Data Protection Officer (DPO)?" Many small business owners ask this question when thinking about privacy rules. A DPO is someone who…

DORA, or the Digital Operational Resilience Act, is a regulation introduced by the European Union to strengthen the digital resilience of financial institutions. It ensures…

Cyber threats are more sophisticated than ever in today’s digital landscape. Cyberattacks that can expose personal data, bring down operations, and result in financial damage are…

Vulnerability management is a continuous cycle to identify, evaluate, and remedy thevulnerabilities that impact your organization.There is an increasing trend in the number of data…

In the competitive field of cybersecurity, having personnel who are knowledgeable is essential. Watch where you step, you people! Prepare to enter the fascinating field…

Explore a comprehensive guide to the COSO Framework in 2024. This article provides an in-depth overview, unravelling the intricacies of the COSO Framework, its components,…

Introduction In today's digital landscape, ensuring the safety of an organization's network and systems is of utmost importance. Welcome to the world of 'External Penetration…

Introduction:In today's fast-paced mobile communication landscape, it's like there's a heavyweight showdown going on between RCS (Rich Communication Services) and SMS (Short Message Service). These…

Learn how to report HIPAA violations effectively and protect patient privacy with our comprehensive guide. Explore steps for internal reporting and contacting authorities while understanding…

Introduction Hey there! Have you ever wondered how companies make sure your data is safe when they outsource services like cloud hosting or payroll processing?…

Introduction In today's interconnected digital world, where businesses rely heavily on technology and data, the risk of cyberattacks and data breaches is ever-present. No organization,…

Learn how organizations navigate complex regulatory requirements, data breaches, cross-border data transfers, and more. Check out the article to explore best practices to conquer data…

Discover the critical role of Data Protection Authorities (DPAs) in upholding GDPR compliance. Explore how DPAs oversee and enforce data protection regulations, investigating violations and…

Explore the intricacies of GDPR Article 28 in our comprehensive guide. Understand the vital role of data processors and controllers in data protection. Learn how…

Are you confused about whether to obtain a SOC 1 or SOC 2 for your business? Our article provides a comprehensive comparison of SOC 1…
Introduction: In the modern world, businesses of all sizes are increasingly worried about the rise in cyber threats. As a result, there's a growing demand…
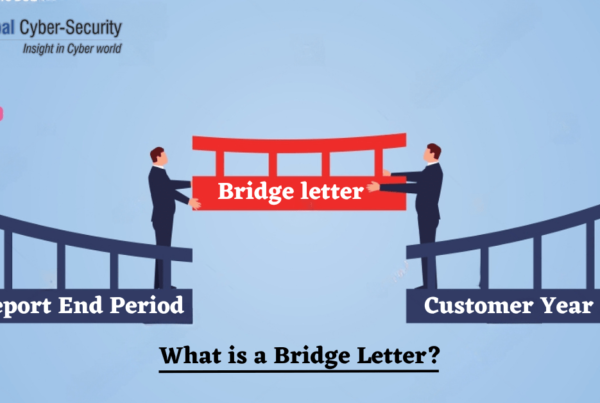
So, you've probably heard about SOC reports and how they're important for businesses, right? But if you're going through a SOC Attestation for the first…

Introduction: In today's world, cyber threats are a growing concern for businesses of all sizes. As technology advances, so do the methods used by malicious…
What is Cryptography ? Cryptography is the process of transforming information into a secure format, known as a ciphertext. Cryptography is majorly used to protect…

INTRODUCTION: The issues that IT companies are currently dealing with are numerous and only get worse with time. They are constantly seeking efficient methods, such…
Introduction Today, we are witnessing an increase in the transition of physical data moving towards digital format. This has pushed the need for implementing strict…


